Computer Architecture and Embedded Systems (CAES) Laboratory
Technical Areas: Computer Architecture, Embedded systems, RISC-V, high performance computing, supercomputing, Edge computing, hardware root-of-trust, system-on-chip design.
Current Projects

BGAS/Zeno: Capability-Aware System Design Prototype
Despite the efforts for numerous security researchers, memory safety vulnerabilities continue to plague modern computing systems
Capability-based systems attempt to solve this safety violation by validating access permissions in hardware. However, the high performance cost associated remains a hindrance to adoption in existing capability-based systems
Under this research effort, the team introduces a new way of building memory-safe systems that can fulfil modern high-performance compute requirements.
The system includes elements from all stages of the compute stack that enables development of memory-safe applications including processors, compiler, operating system, and runtime support libraries.
The system includes the following subprojects: Zeno, CORDON, RAIL, Panoptes, and SecProbe.

Hardware-assisted secure HPC/data-center scale shared memory: Zeno is a new security-aware scalable architecture for shared, distributed memory, high performance computing (HPC) systems. Its micro-architectural support for shared memory enables security-aware data sharing between different processors in a single HPC system without hindering scalability.
Zeno Processor: A Secure High-Performance Computing RISC-V Processor Design
The traditional evolution of the HPC field has created an ecosystem where oftentimes a small number of systems would be commissioned by a government agency through a computer system vendor using (i) proprietary intellectual property (IP) blocks and (ii) obscure or rigid system architecture.
One can argue that the lack of open-architecture concepts in HPC and server-class systems has severely hindered innovation in the field. System-level security-related research efforts are generally altogether abandoned due to the lack of visibility or access to micro-architecture details to test, analyze or validate vulnerabilities, threats or risks.
Under this research effort, the team has introduced a new open-source server architecture, called Zeno, where high-performance and security are both first class system characteristics.
The Zeno architecture specifications, synthesized design, system support software, and programming tools will be open-sourced.
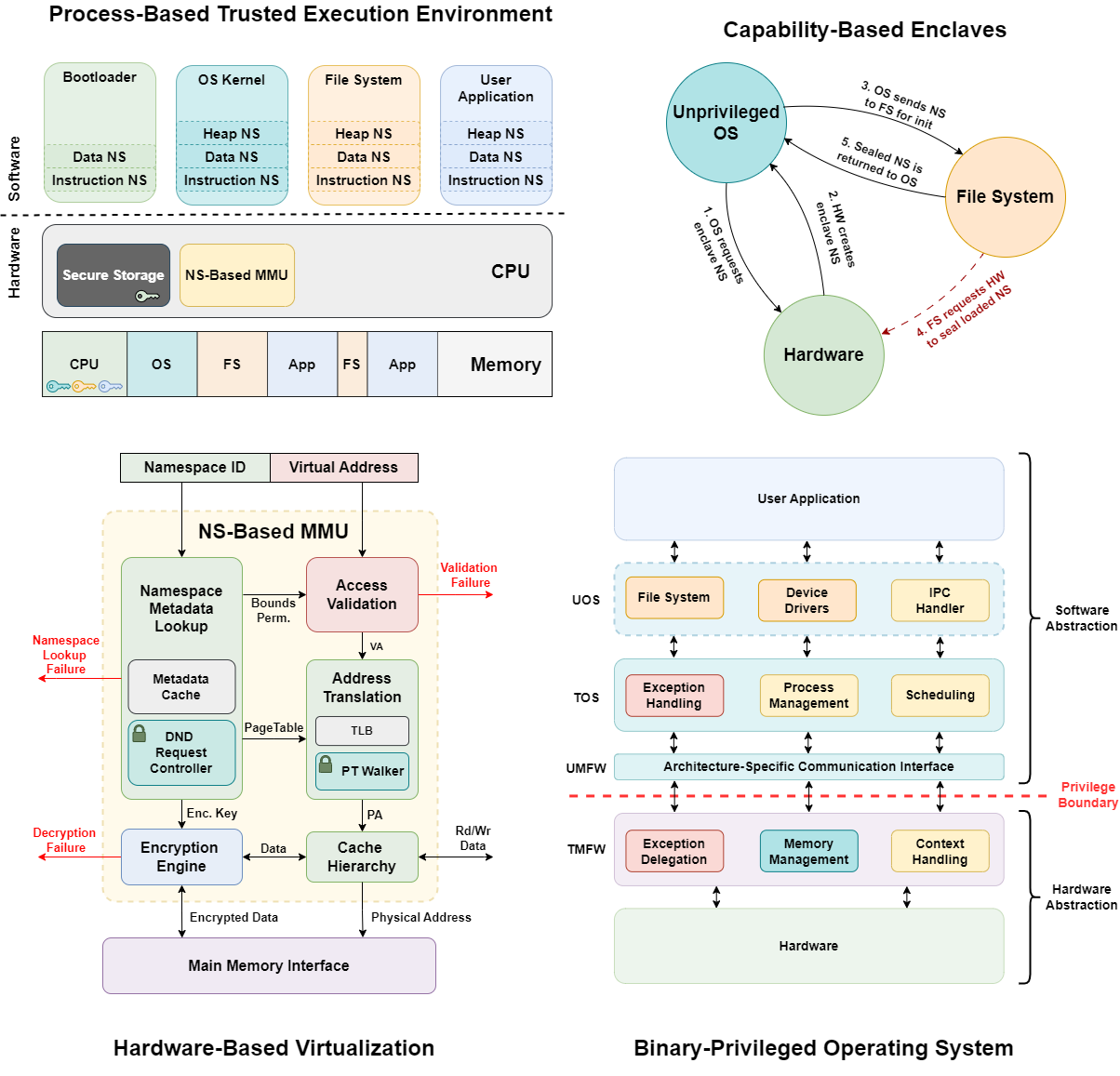
CORDON: Capability-Aware Microkernel and Trusted Execution Environment
Current trusted execution environments (TEEs) protect applications from privileged software but remain limited by rigid abstractions and kernel-mediated trust. VM-based designs offer coarse isolation, while enclave-based systems rely on static memory partitioning and kernel coordination, restricting scalability and fine-grained sharing.
CORDON rethinks this model by introducing process-level isolation built entirely on hardware-managed capabilities. Each process executes within its own sealed Namespace, a hardware-validated domain that enforces permissions, bounds, and confidentiality independently of the operating system. This eliminates the need for kernel cooperation in enforcing isolation or mediating communication.
CORDON’s capability contracts provide a runtime mechanism for secure delegation, revocation, and cross-process function calls, enabling fine-grained collaboration among mutually distrusting components. The design combines a minimal trusted computing base with a microkernel-style software stack that supports distributed operation without relying on privileged monitors.
CORDON serves as a foundation for scalable, capability-oriented TEEs that unify process isolation and secure delegation under a common hardware abstraction.

R-Visor provides a modular, highly extensible platform with a user-friendly instrumentation API, supporting diverse instrumentation capabilities.
R-Visor: Dynamic Binary Instrumentation and Analysis Framework for Open Instruction Set Architectures
Binary Instrumentation (BI) is a technique that involves altering an application binary to include new instructions termed instrumentation code. This has a wide range of utility such as emulation of new instructions, profile collection for binary optimization, malware detection and binary translation from one architecture to another.
Despite BI being a mature field, its advancements have been targeted at closed ISAs such as X86 and ARM, although there has been a recent surge of interest in open ISAs such as RISC-V due to their extensibility feature. However, traditional instrumentation tools, built for closed ISAs, lack the adaptability to easily support new extensions. Therefore, a key requirement for modern instrumentation tools is easy extensibility.
R-Visor is an extensible modular dynamic binary instrumentation (DBI) tool designed for open Instruction Set Architecture (ISA) ecosystems, facilitating architectural research and development. R-Visor addresses the extensibility challenge by leveraging the ArchVisor DSL, which allows users to readily incorporate new ISA extensions. R-Visor is open source, while providing initial support for the RISC-V ISA.

Panoptes: Profiling execution patterns across binaries
Profile Guided Optimization (PGO) leverages runtime execution profiles to improve the effectiveness of compiler optimizations. Despite its utility, PGO is a labor-intensive and time-consuming process. It typically required compiling programs with instrumentation code, executing them (usually multiple times) to gather representative profiles, before finally recompiling them to produce optimized binaries. This multi-stage process suffers from scalability issues, and is usually program-specific.
Panoptes aims to facilitate PGO workflows by learning transferable insights from previously collected profiles. Instead of treating each binary as an isolated optimization problem, Panoptes identifies common patterns across binaries and leverages them to infer effective optimization strategies. To achieve this, Panoptes integrates multiple core capabilities such as:
- Machine learning models for static prediction of execution profiles
- Clustering to promote optimization reuse across binaries
- Bottleneck visualization to facilitate human-guided program optimization

SecProbe standardizes the evaluation of hardware-enforced memory safety, bridging the gap between software testing and architectural security validation.
SecProbe: Evaluating Processor Security Techniques
Most existing efforts to evaluate memory safety focus on software-level schemes such as sanitizers, static analyzers, and compiler-based defenses. While these tools effectively detect vulnerabilities during development, they do not capture how underlying hardware mechanisms contribute to memory safety at runtime. As processors increasingly integrate features like pointer authentication, memory tagging, and capability enforcement, there remains no standardized way to assess their effectiveness across architectures.
SecProbe addresses this gap with a dedicated benchmark suite for evaluating hardware-level defenses against memory safety violations. The suite includes microbenchmarks targeting out-of-bounds reads and writes, buffer overflows, use-after-free, double-free, and heap manipulation, each designed to exercise real enforcement paths in processors.
Designed for portability and minimal system dependencies, SECPROBE ensures consistent, reproducible results across platforms. Each benchmark provides deterministic exploit behavior, enabling precise measurement of detection, prevention, and performance characteristics of hardware-supported protection mechanisms.
Publications
- Edwin Kayang, Mishel Jyothis Paul, Eric Jahns, Muslum Ozgur Ozmen, Milan Stojkov, Kevin Rudd, and Michel A. Kinsy: “R-Visor: An Extensible Dynamic Binary Instrumentation and Analysis Framework for Open Instruction Set Architectures”, In Proceedings of the 26th ACM SIGPLAN/SIGBED International Conference on Languages, Compilers, and Tools for Embedded Systems (LCTES). Association for Computing Machinery, New York, NY, USA, 2025.
- J. Abraham, A. Ehret, and M. A. Kinsy: “A Compiler for Transparent Namespace-Based Access Control for the Zeno Architecture”, In the International Symposium on Secure and Private Execution Environment Design (SEED), 2022.
- X. Wang, B. Williams, J. D. Leidel, A. Ehret, M. Mark, M. A. Kinsy and Y. Chen: “xBGAS: A Global Address Space Extension on RISC-V for High Performance Computing”, In the 35th IEEE International Parallel & Distributed Processing Symposium (IPDPS), 2021. Best Paper Award
Technical Lead
